Cybersecurity in the Digital Age
/ /
In today’s interconnected world, where technology plays a vital role in our daily lives and business operations, ensuring robust cybersecurity has become paramount. From data breaches to ransomware attacks, cyber threats continue to evolve, posing significant risks to individuals and organizations alike. In this blog post, we will explore the importance of cybersecurity in the digital age, discuss the evolving landscape of threats, and provide valuable insights into safeguarding your data and defending against these challenges.
- The Evolving Cyber Threat Landscape:
- Discuss the ever-changing nature of cyber threats, including malware, phishing attacks, social engineering, and zero-day exploits.
- Highlight the increasing sophistication and persistence of cybercriminals, their motivations, and the potential consequences of cyberattacks.
- Importance of Cybersecurity:
- Explain why cybersecurity is crucial for individuals, businesses, and governments.
- Emphasize the impact of cyber breaches on personal privacy, financial loss, reputational damage, and national security.
- Understanding Common Cybersecurity Risks:
- Identify common cybersecurity risks such as weak passwords, unpatched software, and social engineering tactics.
- Provide examples and real-life scenarios to illustrate the potential consequences of overlooking these risks.
- Best Practices for Cybersecurity:
- Discuss essential cybersecurity practices that individuals and organizations should implement.
- Cover topics like strong password management, regular software updates, network security, and employee training and awareness.
- Protecting Personal Data:
- Provide practical tips for safeguarding personal data, including safe online browsing, secure Wi-Fi usage, and data encryption.
- Discuss the importance of two-factor authentication and the use of reputable antivirus and anti-malware software.
- Securing Business Networks and Infrastructure:
- Explain the significance of network security measures, such as firewalls, intrusion detection systems, and secure remote access.
- Highlight the importance of conducting regular vulnerability assessments and penetration testing.
- Incident Response and Disaster Recovery:
- Discuss the importance of having a robust incident response plan in place.
- Provide guidance on creating backups, implementing data recovery processes, and having a crisis communication strategy.
- Emerging Trends in Cybersecurity:
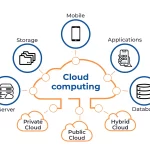
- Explore emerging trends in cybersecurity, such as artificial intelligence for threat detection, blockchain for secure transactions, and cloud security.
- Discuss the potential benefits and challenges associated with these new technologies.
Posted in Blogs